The world’s first behavioural scanning engine — reveals hidden risks before they become breaches.
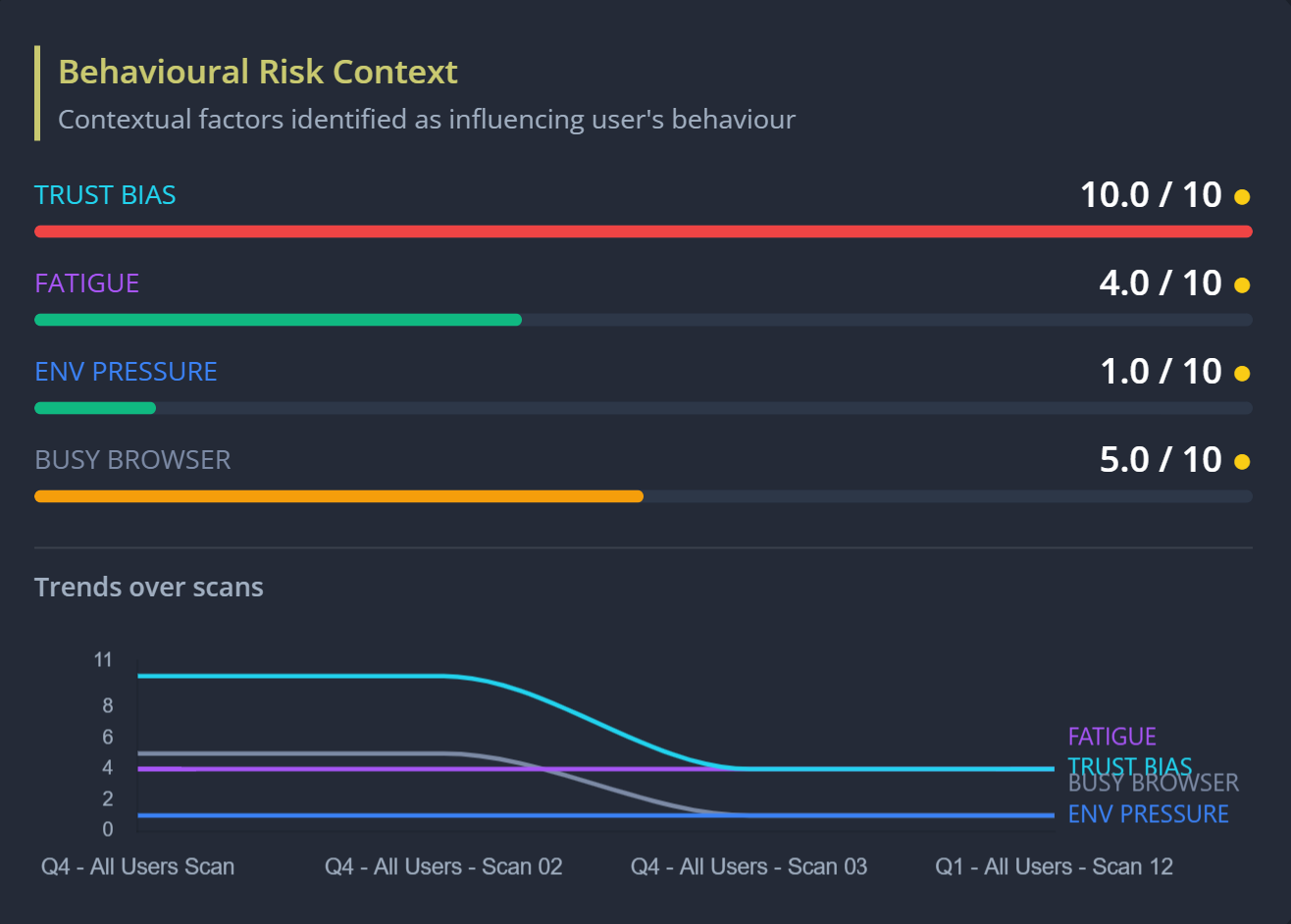
Privci analyses why people behave the way they do, surfacing trust, fatigue, and shortcuts that quietly influence risky behaviours.
Year after year, human behaviour remains the leading cause of data breaches, despite sustained investment in people, processes, and security programmes.
Organisations continue to be compromised in the same familiar ways.
The issue is not a lack of awareness, but a failure to understand the underlying conditions — trust, fatigue, and normalised shortcuts — that shape behaviour long before incidents occur.

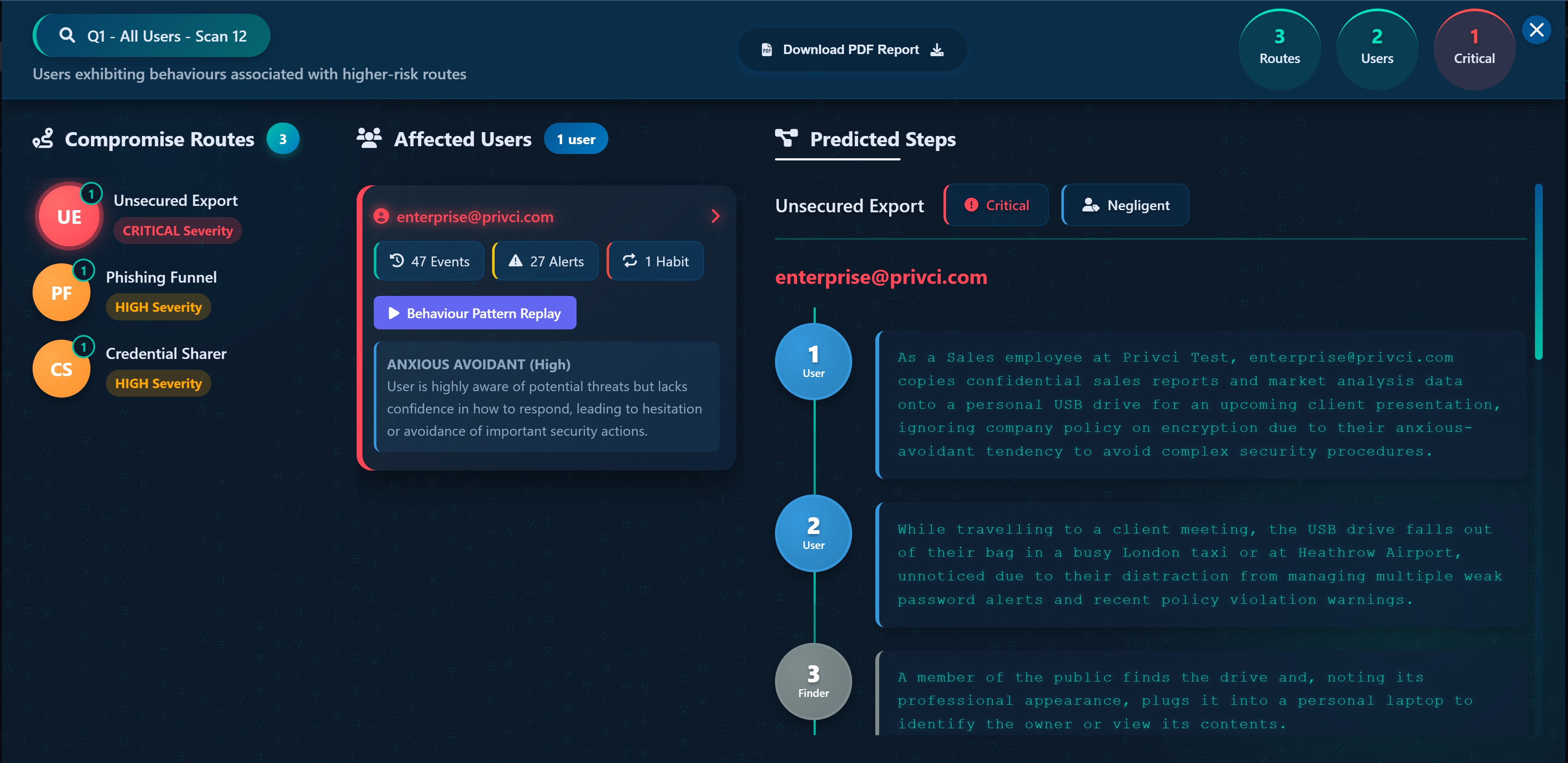
Privci’s Human Vulnerability Scanner surfaces the behavioural conditions that shape risk across organisations, providing clear visibility into patterns, pressures, and norms that create routes to compromise.
Think of a traditional security scanner. It maps your network, identifies unpatched systems, and highlights technical vulnerabilities. Privci’s Human Vulnerability Scanner does the same — but for people. It uncovers the trust, fatigue, pressure, and everyday context that quietly shape how employees make decisions, long before those decisions are exploited.
We call the engine behind the Scanner APIR—Assess, Personalise, Intervene, and Reassess. It’s a continuous loop that turns human behaviour into something you can actually measure and improve.
The Scanner starts by understanding how your organisation really works, using your internal policies as a baseline. Over a period of 15 to 90 days, it observes day‑to‑day behavioural signals to build a realistic picture of what’s happening across the organisation.
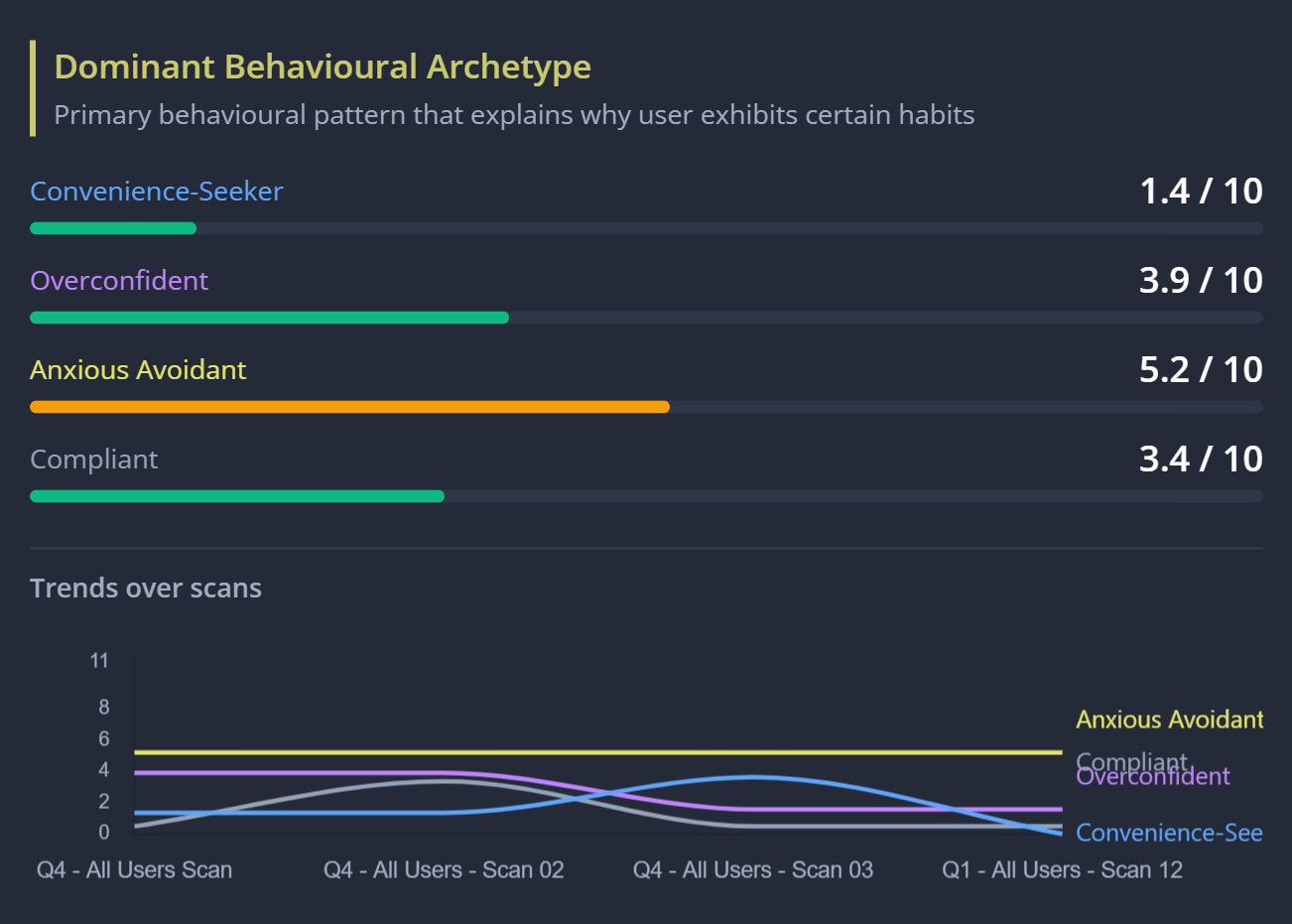
Personalise is where those signals are interpreted. The Scanner doesn’t treat everyone the same. Two people might take the same action for very different reasons — one driven by trust, another by time pressure. Without understanding that difference, any response will miss the mark.
Intervene is where insight turns into action. Rather than delivering a static report, the Scanner deploys specialised intervention agents that provide the right support to the right people — whether that’s a convenience‑seeker, an anxious avoidant, or a behavioural norm shaping group behaviour.
Reassess ensures the Scanner continues to improve over time. The system learns from every interaction — what changed behaviour, what didn’t, and where risk remains — refining its understanding with each cycle and continuously adapting to strengthen insight and effectiveness from one scan to the next.
The experience is simple. It runs right in the browser — no software to install and no disruption to daily work. It’s fast to deploy, easy to scale, and non‑intrusive, presenting itself as a personal assistant rather than a security control, offering guidance, reminders, and support in context.

So what does the scan reveal?
The scan provides a clear behavioural map of your organisation. Each employee receives a Vulnerability Profile highlighting strengths, risky habits, the factors influencing behaviour, and the primary behavioural pattern driving those habits.
Across teams, you gain visibility into dominant archetypes and behaviours that have become normalised — making it clear where attention is needed.
But the real power lies in the routes to compromise — showing exactly how specific behaviours could be exploited by an attacker.
That’s insight you can act on — across the business, not just security.

Explore Privci in action with interactive demos that offer a practical look at how the Scanner uncovers hidden behavioural risk across organisations.
Behaviour‑driven human risk management for every organisation. Start with a free 30-day Human Vulnerability Scan.
Perfect for small teams beginning their human‑risk journey.
Designed for organisations ready to automate behaviour change.
For large organisations with advanced security, compliance, and integration needs.
Our platform brings together six specialised engines that work in unison to cover the full spectrum of human risk, forming a continuous, adaptive defence system.
Multi-layered training experience designed for modern workforces with diverse needs and behavioural patterns.
Instead of relying on one‑size‑fits‑all annual training, Privci provides continuous, contextual, and adaptive learning across three core training streams.
Meets mandatory training requirements, reduces repeat violations by 67%, cuts training costs by 45%, and strengthens security culture with measurable behavioural change.
Transforms behavioural data into targeted interventions using the COM‑B model for sustainable change.
While the Awareness Engine delivers training and behavioural data, the Change Engine transforms that data into targeted behavioural interventions addressing root causes of risky habits.
Dedicated phishing‑resilience module combining automated simulations with gamified skill‑building.
Phish Aware goes beyond traditional phishing campaigns by combining Phish Tests with the more advanced Phish Challenge, offering a deeper, more accurate assessment of user strengths and weaknesses.
Digital footprint analysis and real‑time enforcement to prevent data loss and monitor exposure.
Business Watch focuses on each user's digital footprint, online exposure, and data protection, providing a critical assessment layer that works standalone and also feeds into both the Behaviour Change Engine and the Human Vulnerability Scanner.
Transform your internal security policies into actionable guidance and measurable compliance.
Privci's policy-driven design is rooted in a simple principle: help organisations reduce cost, effort, and administrative overhead by making the most of their internal security policies.
Automatically gathers, structures & maps human‑behaviour and admin evidence across 7 major frameworks.
Eliminate the manual, time‑consuming process of gathering audit evidence. The Compliance Engine continuously collects platform‑generated behavioural and administrative data—policy acknowledgements, training completions, phishing results, DLP alerts, and more—and maps it directly to the specific controls of SOC 2, HIPAA, ISO 27001, NIST CSF, PCI DSS, Cyber Essentials+, and GDPR.
Reduces manual evidence gathering by up to 80%, accelerates audit preparation, and cuts external consulting costs by delivering instant, auditor‑ready compliance packages aligned to the most common international standards.