Human Vulnerability Scanner
Uncovering Hidden Vulnerabilities Traditional Tools Overlook
Transforming the human element of security through evidence-based behavioural interventions
Executive Summary
Privci is a research‑driven platform — the Human Vulnerability Scanner — designed to address the human element of cybersecurity at a deeper, more scientific level. Instead of treating security as a training problem, Privci focuses on sustainable behavioural change through targeted, evidence‑based interventions.
Our approach combines behavioural science, psychology, and AI to uncover the trust, fatigue, pressure, and everyday context that quietly shape how employees make decisions — long before those decisions are exploited.
The Scanner enables organisations to identify:
The Scanner
Our methodology is operationalised through a structured, cyclical framework called APIR (Assess, Personalise, Intervene, Reassess), creating a continuous feedback loop that strengthens security behaviour over time.
Continuous synthesis of behavioural signals, organisational policies, and threat intelligence to build dynamic behavioural profiles.
Advanced behavioural modelling across individual and archetype layers to enable context‑aware risk assessment.
Targeted interventions selected from 10 specialised Direct Interventions, powered by an AI‑driven reasoning layer.
Ongoing evaluation using reinforcement learning to refine intervention strategies for each behavioural profile.
The Training Agent
The central component of Privci operates continuously in the background, using lightweight, browser‑based agents to observe and measure how employees respond to real, contemporary cyber threats.
For employees, the experience is simple. It runs directly in the browser — with no software to install and no disruption to daily work. The agent is fast to deploy, easy to scale, and non‑intrusive, presenting itself as a personal assistant rather than a security control. It provides guidance, reminders, and support in context.

Behavioural Intelligence
Archetype Distribution
The scan provides a clear behavioural map of your organisation, both at an individual and team level. This visibility into dominant archetypes and normalised behaviours makes it clear where attention is needed and why risk manifests the way it does.
Why risk manifests the way it does
Measures individual susceptibility to security threats
Quantitative organisational exposure to specific threats
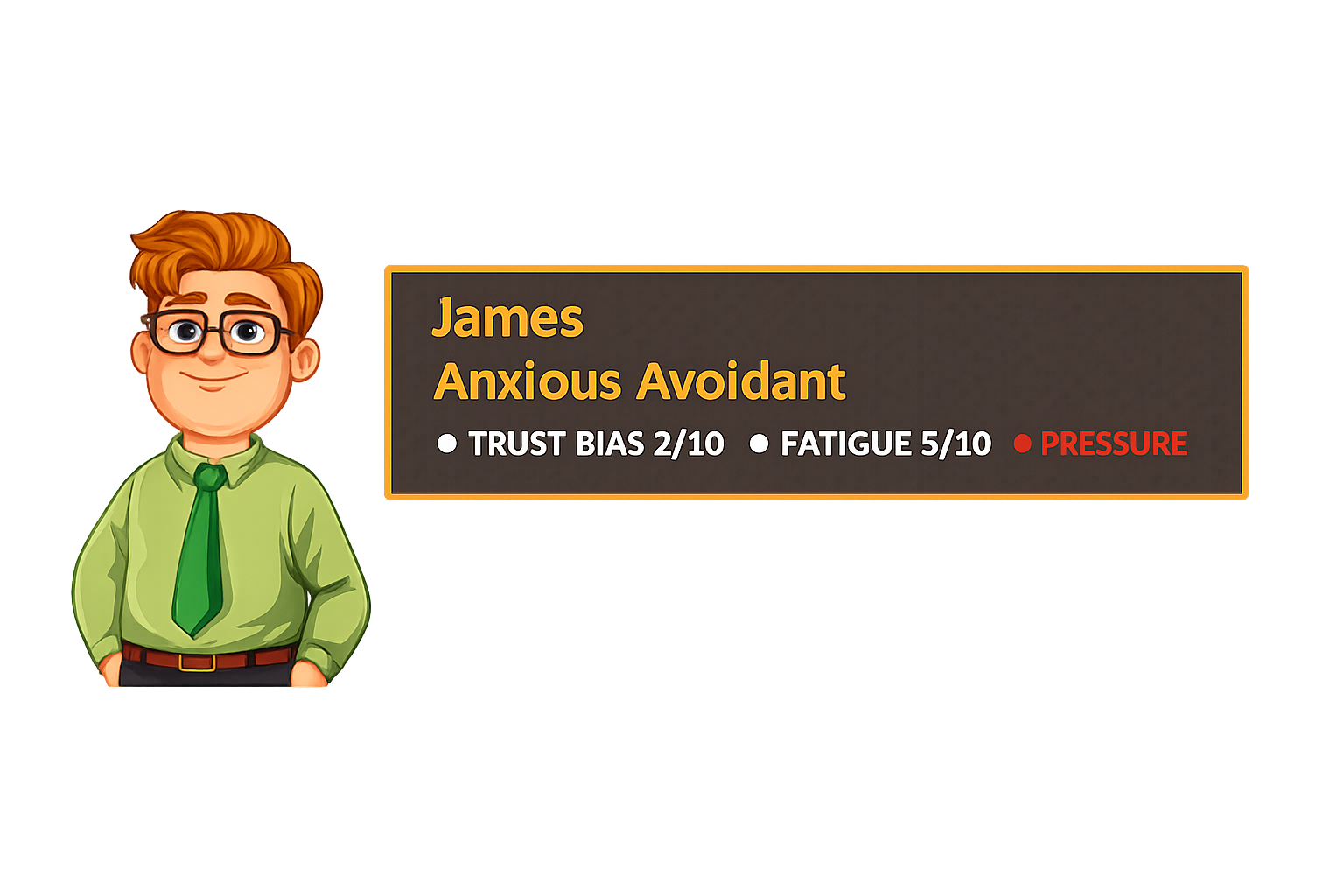
Primary behavioural pattern that explains why user exhibits certain habits
Contextual factors identified as influencing user's behaviour
Compromise Routes
Beyond organisational mapping, the Scanner identifies realistic routes to compromise – step‑by‑step attacker pathways that exploit observed behavioural patterns. This shows exactly how an attacker could chain seemingly minor behaviours into a full‑scale breach, and where intervention is most effective.
Example: Social Engineering Route
This route — identical to the M&S and Co‑op attacks — is flagged when the Scanner detects users likely to bypass verification or trust unsolicited contact. It doesn’t just identify who is at risk; it shows the exact path an attacker would take.
Each route includes actors, methods, and potential business impact – from credential theft to data exfiltration.
Routes are generated dynamically based on actual observed behaviours, not hypothetical threat models.
Understanding the exact sequence enables precise interventions at each vulnerable point, stopping attacks before they succeed.
Interventions
Our interventions are grounded in the COM‑B model of behaviour change, enabling us to understand a user's Capability, Opportunity, and Motivation—the three essential components for sustainable behavioural change.
Capability
Do users have the knowledge and skills required?
Opportunity
Does their environment make it easy (or even possible) to do it?
Motivation
Do they want to do it, and do they see the value in doing it?
Behaviour Change
Users consistently adopt secure cybersecurity practices.
The psychological and physical ability to engage in secure behaviour. Includes knowledge, skills, and understanding of security protocols.
External factors that make secure behaviour possible. Includes organisational policies, tools, and environmental cues that support security practices.
Brain processes that energise and direct behaviour. Includes both reflective (planned) and automatic (habitual) motivation for security practices.
The Privci Engines
Our platform brings together six specialised engines that work in unison to cover the full spectrum of human risk, forming a continuous, adaptive defence system.
Transforms internal security policies into actionable guidance and training resources
Multi-layered training across three streams with real-time correction and gamified learning
Transforms behavioural data into targeted interventions using COM‑B model
Dedicated phishing‑resilience module with 800+ templates and gamified challenges
Digital footprint analysis with real‑time enforcement and dark web monitoring
Auto‑maps human‑behaviour & admin evidence to 7 frameworks
Policy Keeper
Transforms internal security policies into actionable guidance with 120+ customisable templates. Centralised Policy Hub with real-time tracking and audit‑ready evidence.
ROI: Automates manual processes, reduces administrative overhead by 60%, ensures complete accountability.
Awareness Engine
Multi-layered training across Baseline, CyberSkills, and Policy Training streams with real-time correction and gamified learning.
ROI: Reduces repeat violations by 67%, cuts training costs by 45%, meets mandatory compliance requirements.
Change Engine
Transforms behavioural data into targeted interventions using COM‑B model. Includes Behaviour Change with 10 Direct Interventions.
ROI: Moves from "training delivered" to "risk reduced," prevents incidents before escalation.
Phish Aware
Dedicated phishing‑resilience module with 800+ templates, Live Template Suggestions, and gamified Phish Challenge.
ROI: Reduces successful phishing attacks by 85%, meets PCI DSS, HIPAA, ISO 27001 requirements.
Business Watch
Digital footprint analysis powered by Exposure Scan, Data Geofencing, Browser‑Based DLP, Data Guard (real‑time enforcement), and Dark Web Search for leaked credentials.
ROI: Identifies Shadow IT risks, prevents browser‑based data leakage, provides early credential breach detection.
Compliance Engine
Automatically gathers, structures, and maps human‑behaviour and administrative evidence across 7 major frameworks — SOC 2, HIPAA, ISO 27001, NIST CSF, PCI DSS, Cyber Essentials+, and GDPR.
ROI: Delivers instant audit‑ready evidence out of the box, reduces manual effort by up to 80%, accelerates audit readiness, and significantly lowers external consulting costs.
ROI Analysis & Financial Impact
Privci delivers measurable financial returns through reduced incidents, lower training costs, improved operational efficiency, and dramatically faster audit preparation. The Compliance Engine alone cuts manual evidence gathering by up to 80% and provides instant, auditor‑ready compliance packages across seven frameworks.
Quantifiable Benefits
Cost-Benefit Analysis (Sample 500-person organisation)
| Metric | Before Privci | After Privci | Improvement |
|---|---|---|---|
| Human‑caused Security Incidents | 24 | 6 | -75% |
| Average Cost per Incident | $15,000 | $7,500 | -50% |
| Annual Training & Awareness Spend | $50,000 | $27,500 | -45% |
| Policy & Compliance Admin Time | 120 hours/month | 48 hours/month | -60% |
| Productivity Lost to Security Friction | 10 hours/employee/year | 4 hours/employee/year | -60% |
| Audit Evidence Preparation Time | 80 hours/audit | 16 hours/audit | -80% |
Compliance Framework Alignment
Privci automatically maps human‑behaviour and administrative evidence to major international standards. The Compliance Engine provides up to 50% of required control evidence out‑of‑the‑box, with clear gap disclosure for the remaining technical controls.
Strong support for policy communication, human‑risk assessment, behavioural monitoring, and control activities (Common Criteria).
Administrative safeguards are thoroughly addressed, including policy management, workforce training, risk analysis, and incident plan documentation.
Extensive coverage of organisational and people controls (Annex A.5 & A.6), with browser‑level data protection and incident early‑warning signals.
Strong in awareness & training, human behaviour monitoring, policy management, and browser‑level data security across all six Functions.
Excels in policy management, security awareness, acceptable use enforcement, phishing testing, and user‑activity monitoring.
Policy management, user awareness training, and behavioural monitoring fully covered; technical controls (firewalls, secure config, patching) must be provided externally.
Accountability documentation, staff awareness, organisational security measures, browser DLP & geofencing, and early‑warning breach detection.